Trezor Login – Secure Access to Your Hardware Wallet
Trezor Login is the official process that allows you to securely access and manage your cryptocurrency through a Trezor hardware wallet. By using Trezor Login, users benefit from enhanced security, offline key storage, and a user-friendly interface to send, receive, and store digital assets safely.
Why Trezor Login Matters for Crypto Security
Trezor Login plays a crucial role in securing digital investments. Unlike centralized exchanges, Trezor Login ensures that private keys never leave your hardware device. This makes Trezor Login one of the safest ways to access funds and protect against hacking attempts.
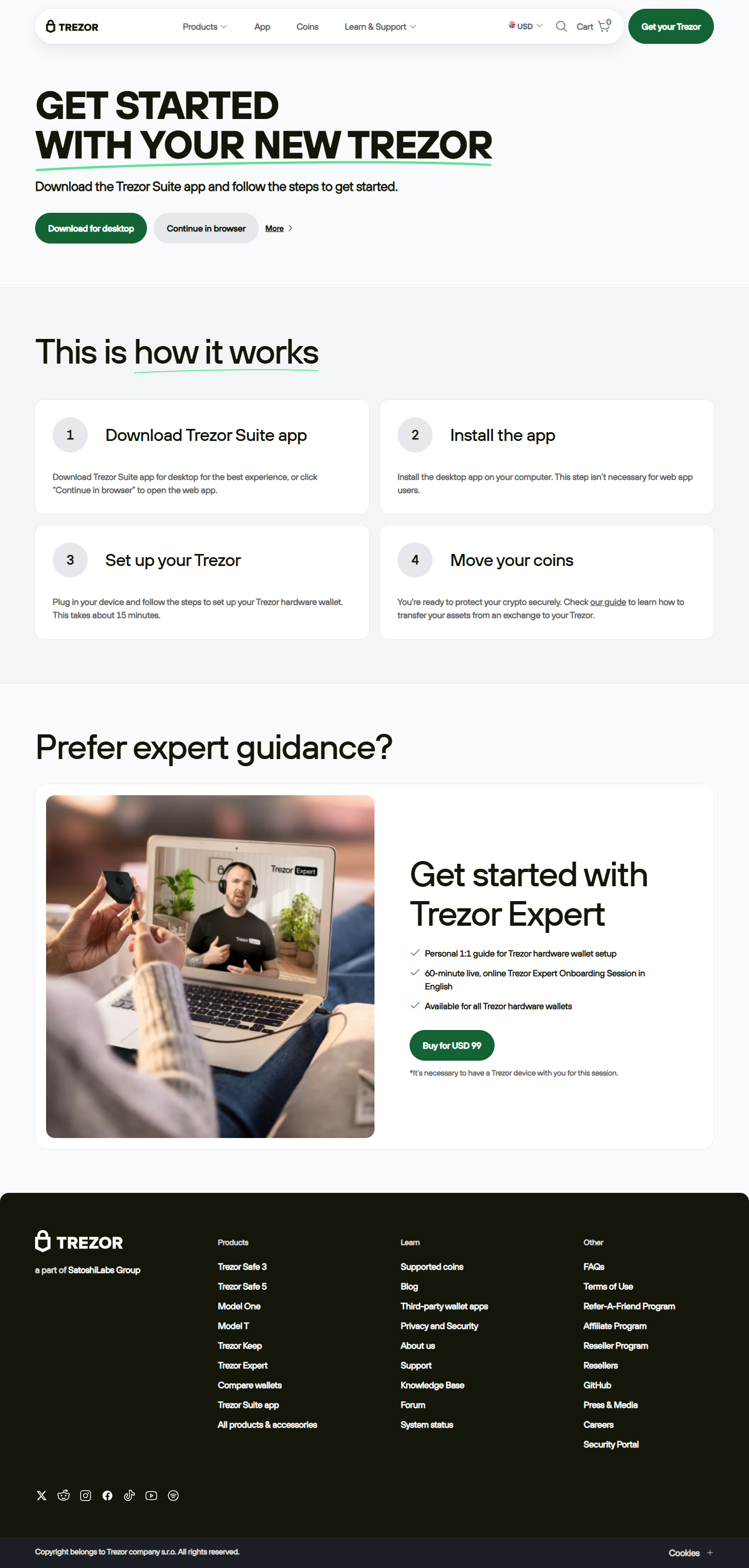
How to Complete Trezor Login Step by Step
Setting up Trezor Login for the first time is simple. Follow the steps below to complete your Trezor Login and start managing your crypto portfolio securely.
- Connect your Trezor hardware wallet to your computer or mobile device to begin the Trezor Login process.
- Visit the official Trezor Suite application or Trezor.io/start to initiate Trezor Login.
- Follow the prompts on-screen and enter your PIN when prompted to complete Trezor Login.
- If required, confirm actions directly on your device to validate the Trezor Login.
- Once authenticated, you can access your dashboard and manage your assets through Trezor Login.
Key Features of Trezor Login
With Trezor Login, users can enjoy multiple security features, including passphrase protection, encrypted access, and compatibility with wallets like MetaMask. The Trezor Login process ensures every transaction is verified on the physical device before being approved.
Trezor Login vs. Exchange Logins
Unlike centralized platforms, Trezor Login does not rely on traditional email and password systems. Instead, Trezor Login is tied directly to your hardware device, giving you total control of your funds. This makes Trezor Login a safer alternative for long-term investors.
Troubleshooting Trezor Login Issues
If you face challenges during Trezor Login, common solutions include updating your firmware, reinstalling Trezor Suite, or checking your USB connection. In some cases, clearing browser cache can also resolve Trezor Login errors quickly.
Best Practices for Secure Trezor Login
To maximize security, always complete Trezor Login through the official Trezor Suite app or website. Avoid third-party sites when performing Trezor Login, and ensure your recovery seed is safely stored offline in case of emergencies.
Why Users Trust Trezor Login Worldwide
Millions of investors worldwide rely on Trezor Login to protect their assets. From Bitcoin to Ethereum and thousands of altcoins, Trezor Login provides a seamless way to interact with blockchain networks while maintaining top-level security.
Conclusion on Trezor Login
In conclusion, Trezor Login is a secure, reliable, and user-friendly gateway to managing digital currencies. By combining hardware wallet protection with intuitive software, Trezor Login ensures that your crypto portfolio is safe and accessible only by you.
Disclaimer: This article on Trezor Login is for educational purposes only and should not be considered financial advice. Always perform Trezor Login through official Trezor platforms. Cryptocurrency investments carry risks, and users should consult a financial advisor before making decisions.